The present article presents a digest of a series of articles describing codes and ciphers used during the American Civil War.
During the Civil War, protection by code/cipher was more important than before because of extensive use of telegraphy. Both sides were aware that without encryption, telegraphic communications were read by the opponent by means of wiretapping (OR records many such references, e.g., vol.16, p.232; vol.23, p.212, 219; and Plum records actual wiretapping activities).
Table of Contents:
Union Codes and Ciphers during the Civil War
Confederate Codes and Ciphers during the Civil War
(See another article for details.)
At the time of the First Battle of Bull Run (21 July 1861), the first major battle of the Civil War, the Union used a cipher that was simple enough to be broken by E.P. Alexander. After the defeat in the battle, General McClellan was called to Washington to reorganize the Union army and he brought with him a cipher which had been provided by Anson Stager when he had been in Ohio. This formed the basis of Union ciphers throughout the war.
The Stager cipher employs route transposition, whereby words are written in a matrix line by line and the ciphertext is formed by taking the words column by column according to a certain route.
A despatch of Buell to Halleck of 29 September 1862 is used here to explain the enciphering process in one version (Cipher No. 7).
First, some words in the message is replaced with code words.
The words are then written in 6 columns and the ciphertext is formed by copying this column by column according to the route shown, adding an extra word after completing each column. The route and the number of columns forms the key, which the recipient should know to decipher. In this example, the route can be specified as: up the 1st (column), down the 6th, up the 2nd, down the 3rd, up the 5th, down the 4th or simply "up 1, down 6, up 2, down 3, up 5, down 4."
| (4)↓ | (6)↓ | (2)↓ | |||
| rapture | September | twenty | nine | 1862 | for |
| olden | ocean | I | have | received | your |
| orders | of | the | twenty | fourth | instant |
| requiring | me | to | turn | my | command |
| to | Camden | I | have | accordingly | turned |
| over | the | command | to | him, | and |
| in | further | obedience | to | your | instructions |
| I | shall | repair | to | Indianapolis | and |
| await | further | orders | alvord | pretty | rough |
| (1)↑ | (3)↑ | (5)↑ |
The resulting ciphertext is as follows.
The first word (called "commencement word") "Austria" indicates 9 lines. The recipient reconstructs the above matrix by copying the words in the message column by column according to the prearranged route, deleting an extra word at the end of each column. Restoring the code words provides the plaintext.
During the war, the Stager cipher developed from a very simple one written on a card into a complicated cipher book consisting of 40 pages of routes and code words. In the meantime, the scheme underwent several significant changes.
In the beginning, unlike the example above, words were written in a matrix column by column according to a certain route and the ciphertext was formed by taking the words line by line. The recipient would write the cipher words line by line in 6 columns (the number of columns was fixed), deleting every 7th letter, and then read the words according to a specified route.
Cipher No. 7 (Note that the numbering was not sequential), introduced within the year 1861, changed this to the scheme of the above example whereby words are written in a matrix line by line and the ciphertext is formed by taking the words column by column according to a certain route. This makes the commencement word meaningful, whereas in the initial version, the recipient did not have to know the number of lines beforehand.
Before Cipher No. 7, there appear to have been other versions (including Cipher No. 6 and another between F.J. Porter and McClellan) of a trial character.
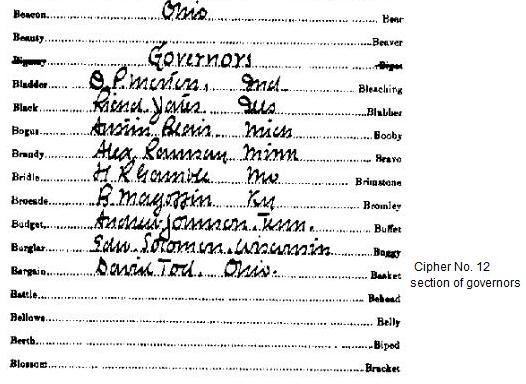
Ciphers No. 9, No. 10, and No. 12, adopted in 1862, were formed on the same template, which printed commencement words (indicators) and arbitrary words (code words), to which specific routes and meanings were handwritten for respective versions. The commencement word indicates the number of lines (3 to 10), combined with the number of columns (4 to 7). The number of arbitrary words was substantially increased to about 800 (since most entries are given two arbitraries, the number of entries is about 400). The printed words are somewhat out of alphabetical order, which would confuse the eavesdropper, while still manageable for authentic users.
Of the next series, Cipher No. 1 came into general use in February 1864 and was used at least as late as April 1865. Cipher No. 2 was not so generally held but was used at least in June 1864. These were formed on the same template as for Cipher No. 9, No. 10, and No. 12. While the previous series listed three routes for each number of lines, this series simplified it by listing one route for each number of columns. Thus, the indicator now consisted of two words: the first indicating the number of columns and the second indicating the number of lines. (Since the line indicator words are different for each page corresponding to a specific number of columns, the line indicator word suffices for specifying the page and thus the number of columns, making the column indicator redundant.) While the same arbitrary words were used as for the previous series, the vocabulary was somewhat enlarged by assigning only one arbitrary instead of two to many entries, though important names/words were given three or more.
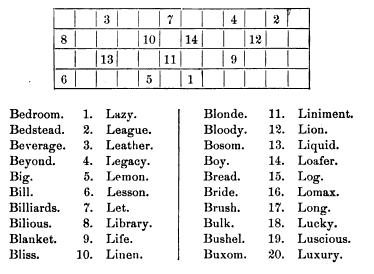
The next series, Ciphers No. 3, No. 4, and No. 5, were formed on a new template. Cipher No. 4 was used at the last stage of the war, while Cipher No. 5 was sent out on 20 June 1865. Now, the redundant column indicator is gone and the single indicator indicates the number of lines (1-20) as well as the specific page devoted to a specific route. The route is shown by a table in which only the numbers in the top row and bottom row are significant. (The numbers represents columns, not the order. The following example indicates a route "up 6, down 3, up 5, down 7, up 1, down 4, down 2".)
Apart from the above, there were also versions specific to particular departments.
Route transposition by word is not a very secure way of secret communication. Any pair of words likely to come one after another would give a clue to the transposition pattern. Later Stager ciphers relied more and more on code words ("arbitrary words") for security. For example, late Stager ciphers had entries for frequent word combinations such as "Has (or Have) arrived", "Has (or Have) been", "In front of", "in order that", etc. (No. 4). (One version even prescribes that if most of the words are replaced with arbitraries, the route transposition may be discarded and the omission is to be indicated by the word "Discarded" at the beginning of the ciphertext.)
The code section of the Stager ciphers lacked means to spell words not in the list. Such words/names were left unencoded or represented by combination of similar sounding syllables/words. In one instance, "Gettysburg" was encoded as "get ties large", in which at least the ending "-burg" is represented by a code word "large." In another instance, "rapidity" was represented by "rape ditty" (see another article). Such phonetic and other irregular spelling was commonly used by cipher operators. Although this kind of usage may avoid the weakness of the nomenclator (i.e., if the size of the code is small, an encoded text has many "spelt" portions, which may be exploited by a codebreaker), it might have posed a riddle even to an authentic recipient.
(See another article for details.)
The Confederates appear to have used simple substitution cipher for a long time after the Civil War began. As late as 9 April 1862, shortly after the Battle of Shiloh, General Beauregard used a simple cipher of "putting the last half of the alphabet first, that is, substituting M for A, N for B, O for C, etc." (which seems to be what is known as "rot13" today). It was deciphered by the Federals and publicized in a New York newspaper.
Rose Greenhow, Confederate spy in Washington, was also given a simple substitution cipher at the beginning of the war. (It appears to have included some 30 additional symbols but they were not fully used.) (See another article.)
In February 1863, Seddon, Confederate Secretary of War since November 1862, thought of using the simplest Caesar cipher. Although, apparently, the proposal was not taken seriously by Robert E. Lee at this time, Seddon, frustrated by a complex cipher, again reverted to a simple substitution cipher in June 1863.
Cipher letters of December 1863 from J.H. Cammack, a Confederate conspirator in New York, to Richmond employed a hieroglyphic substitution cipher. Although it used six different alphabets, it was deciphered by War Department cipher operators in Washington.
(See another article for details.)
In the spring of 1862, Confederate President Jefferson Davis arranged a dictionary code with A.S. Johnston and J.E. Johnston. The dictionary used is A Primary-School Pronouncing Dictionary of the English Language, abridged from the American Dictionary of Noah Webster, LL.D. by William G. Webster (1857). In April 1862, J.E. Johnston used this in a message to Robert E. Lee but it appears the latter used a different dictionary and could not read it.
(See another article for details.)
In May 1862, the Confederate Signal Corps, attached to the Department of the Adjutant and Inspector-General (S. Cooper), was established under William Norris and provided a Vigenere cipher for the army and the government. It was called "the signal corps cipher" or "the government cipher." It appears to have been prepared by E.P. Alexander some time before this.
Vigenere cipher is a polyalphabetic cipher whereby the alphabet to be used for enciphering is selected from a table (Vigenere table or "alphabet square" as sometimes called) for every letter being enciphered according to a keyword.
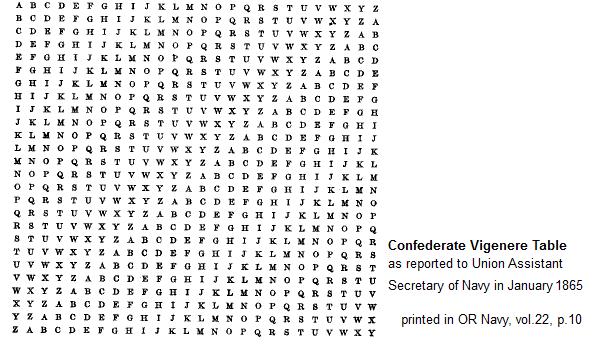
When enciphering "the president" with a keyword "complete victory", first, keyword letters are written over the letters of the plaintext. To encipher, the first letter "t" of the plaintext is found along the leftmost column and the first letter "c" is found along the top row. The intersection between the row headed by "t" and the column headed by "c" indicates the cipher letter "v".
To decipher, the process is reversed. That is, the first letter of the cipher text ("v") is located along the column headed by the first key letter ("c") and far left on that row where "v" is found, the plaintext letter "t" is found.
The Vigenere cipher can be easily updated or adapted simply by selecting a different keyword.
While the Vigenere cipher can be practiced with the alphabet square written on a piece of paper, the Confederate also used physical devices such as a cipher cylinder, a cipher machine/cipher box, or a cipher disk.
The earliest example extant appears to be the despatch of General Kirby Smith of September 1862 (during the Confederate offensive in east Tennessee), probably addressed to General Bragg. The keyword was "Baltimore."
Apart from this single instance, the records of use of the Vigenere cipher generally began in December 1862 or early 1863. Throughout the Vicksburg campaign from December 1862 to July 1863, the keyword "Manchester Bluff" (15 letters) was used by General Pemberton defending Vicksburg and General J.E. Johnston, commander of the theatre attempting its relief. S. Cooper, Adjutant and Inspector-General, also started to use Vigenere with J.E. Johnston in December 1862. President Jefferson Davis switched to Vigenere possibly about the same time (by May 1863 at the latest). Seddon, Secretary of War, appears to have started using Vigenere in February 1863 with Robert E. Lee. Some time before 6 August 1863 (probably after the surrender of Vicksburg on 4 July), the key for "all the military departments" (probably "Manchester Bluff") was replaced.
As of August 1863, the government cipher with a keyword "My Old Kentucky Home" (17 letters) was used by General Buckner (possibly within his own department), who was from Kentucky. Generals Samuel Jones and W. Preston appear to have acquired the cipher about this time.
As of 2 December 1863, a keyword "Ten ..." (if 15 letters, could this be "Ten Commandments"?) had just been replaced, possibly after the major defeat at the Battle of Lookout Mountain.
About March 1864, General Magruder used a keyword "Our Destiny is One" (15 letters) with Richmond. At the same time, a department key "The Heaven ..." was also in use. General Polk proposed a keyword "Fight and Conquer" (15 letters) to J.E. Johnston.
A keyword "Complete Victory" (15 letters) was used at least from July 1864 to March 1865. It was shared by at least Jefferson Davis, Kirby Smith, R.E. Lee, S.D. Lee, J.G. Walker, and Alexander Lawton.
Another keyword "Come Retribution" (15 letters) was used by Jefferson Davis, R.E. Lee, J.E. Johnston, and Breckenridge at least in February and April 1865.
A keyword "Frederika Bremer" (15 letters) was used for signalling with flags (or torches at night) around Charleston from October or November 1864.
The Vigenere cipher was also used by diplomats. The present author recovered a keyword "Where Liberty Dwells, There Is Our Country" used in letters between John Slidell, a commissioner of the Confederacy to France, and J.P. Benjamin, Confederate Secretary of State.
The Vigenere cipher was also used by agents sent to Canada in May 1864.
(See another article for details.)
Secretary of the Navy Mallory used dictionary code with his commanders from a very early stage of the war. For example, if the word "ship" is the 26th word on page 674, it is encoded as "(674)26", "674-26", or the like.
James H. North, who was ordered to go to England to purchase an ironclad warship in May 1861, used Cobb's Miniature Lexicon in his correspondence with Mallory.
Commander Semmes could not find Cobb's Miniature Lexicon in New Orleans and chose Reid's English Dictionary in June 1861.
Later, it appears Mallory did not specify a dictionary and let commanders choose their own. In February 1863, Lieutenant Barney, commanding CSS Harriet Lane, chose Webster's Dictionary.
(See another article for details.)
George T. Sinclair, ordered in May 1862 to go to England to construct or purchase a ship, used a keyed rotating grille in his despatch of 8 August 1863. It differs from the usual rotating grille in that only a part of the matrix specified by a keyword is used.
The present article is a digest of the following series of articles, which are referred to for more details and references.
Development of Stager Ciphers during the Civil War
A Civil War Dispatch Redeciphered
Semi-phonetic Reversal Cipher used in Lincoln's Telegram
Confederate Ciphers during the Civil War: Various Vigenere Keywords
Confederate Ciphers (Other Than Vigenere) during the Civil War
Keyed Rotating Grille Used by Confederate Agent Sinclair during the Civil War
Rose Greenhow's Cipher Letter Written after the First Battle of Bull Run (1861)